In the world of Australian IT, Local Admin has historically been treated like a corporate birthright. For years, many organizations avoided restricting administrative privileges because it was perceived as easier than dealing with the flurry of helpdesk tickets that arrived every time an employee needed to update a specialized application or install a printer driver. But in 2026, that convenience-first mindset is not just a nuisance, it’s a massive liability that’s keeping CISOs awake at night.
As the Australian Signals Directorate (ASD) continues to sharpen its focus, Restricting Administrative Privileges has emerged as perhaps the most culturally sticky part of the Essential Eight. It’s the one control that usually gets the most pushback from staff. Why? Because it feels like a demotion.
But if we look at the data from recent breaches across Sydney and Melbourne, the pattern is undeniable, attackers do not break in anymore; they log in. And once they’re in, they are hunting for those elevated rights to finish the job.
Why ‘Standard User’ is the New Gold Standard
In the current threat landscape, a local admin account is essentially a high-speed lane for ransomware. When we talk about Restricting Administrative Privileges, we are not just trying to be the department of no. We are actively shrinking the field of play for an adversary.
Think about the lifecycle of a typical credential breach. An employee clicks a link in a convincing phishing email. If that employee is running as a standard user, the malware is effectively trapped. It can’t easily disable the EDR, it can’t reach into the LSASS memory to perform Credential Harvesting, and it certainly can’t spread across the network like wildfire.
However, give that same user administrative rights, and you’ve just handed the keys to the getaway car to the thief. Suddenly, that single click turns into a domain-wide catastrophe. This is why Essential Eight Access Control is not a nice to have, it is the literal foundation of a resilient network.
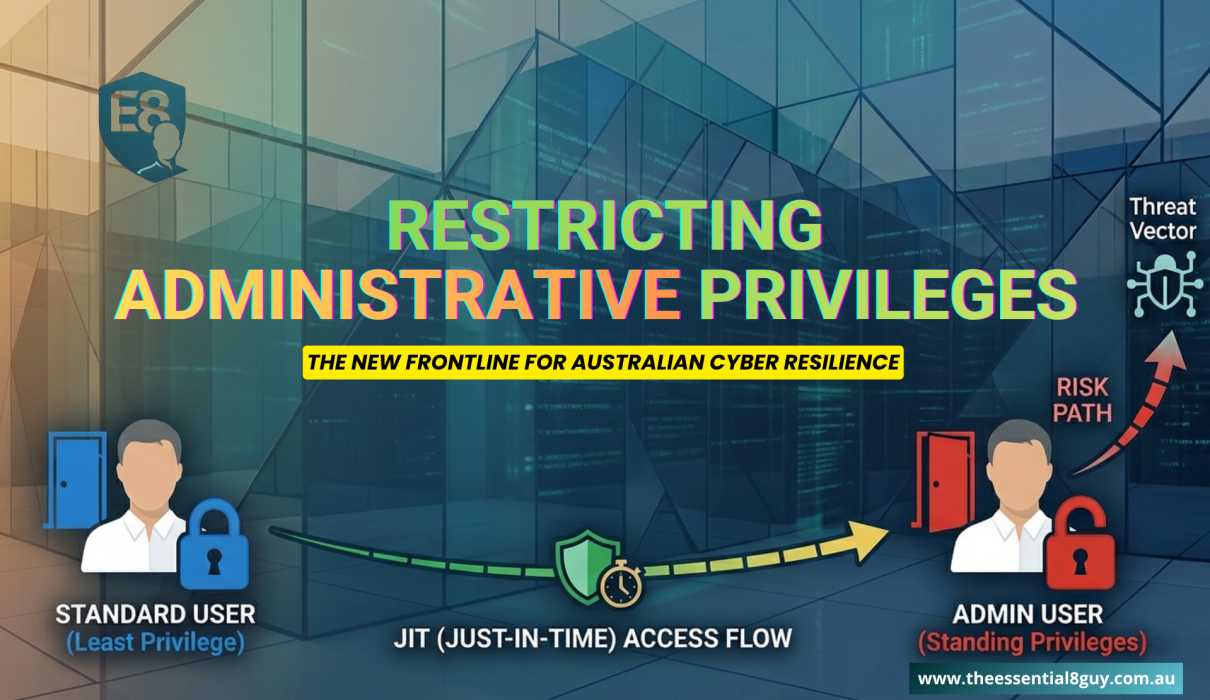
The Strategy – Moving Toward Just-in-Time Access Australia
One of the biggest shifts we have seen recently is the move away from standing privileges. In the old days, an IT manager would have one account that was a Domain Admin 24/7. That is a massive risk. If that account is compromised at 2:00 AM while the admin is asleep, the attacker has hours of unrestricted access.
This is where Just-in-Time Access Australia comes into play. The modern approach and what the ASD expects at ACSC Maturity Level 2 and above, is that nobody has permanent admin rights. Instead, you use a “request and approve” model.
If you are still mapping out your broader compliance journey, check out our deep dive on Essential 8 Maturity Level 2, where we break down how these access controls fit into the wider 2026 security landscape.
How it looks in the real world
Imagine a senior engineer needs to make a configuration change on a production server. Instead of logging in with a permanent admin account, they log in as a standard user and request elevation via a tool like Entra ID PIM (Privileged Identity Management). They provide a reason, maybe a ticket number, and the permission is granted for exactly two hours.
Once the work is done, the rights vanish. If an attacker steals those credentials later that night? They’ve got nothing but a standard user account with no permissions. That is the Principle of Least Privilege (PoLP) in action, and it’s a game-changer for risk mitigation.
Navigating the ‘VIP’ Problem
We have all been there. You try to roll out a restricted access policy, and the first person to complain is the CEO or a Lead Developer. They argue that they’re “power users” and that these restrictions will kill their productivity.
Here’s the hard truth, your VIPs are your High-Value Targets. They are the ones being targeted by sophisticated spear-phishing and social engineering. If anything, they should have the tightest controls.
When I consult with Australian firms on ACSC Maturity Level 2, I always suggest a “top-down” rollout. When the execs lead by example and show that they can do their jobs perfectly fine without local admin rights, the rest of the office tends to fall in line pretty quickly.
The Technical Reality – PAM and LAPS
You can’t just flip a switch and remove admin rights without having the right tools in place to catch the fall. You need a robust Privileged Access Management (PAM) strategy.
For most Australian businesses, the first step is Windows LAPS (Local Administrator Password Solution). It’s a simple, often overlooked tool that ensures every single machine in your fleet has a unique, complex password for its local admin account. It stops the “Pass-the-Hash” attacks that allow hackers to hop from one workstation to another using the same credentials.
Then there is the issue of Credential Harvesting. Attackers love to scrape memory for “hashes” of passwords. If you’ve implemented Restricting Administrative Privileges correctly, you’ve limited the number of places those high-value hashes even exist. You are essentially making the “treasure map” much harder for the bad guys to read.
The Business Side – Tenders, Insurance, and Growth
Let’s step away from the tech for a second and talk about the bottom line. Cybersecurity is not just an IT cost anymore, it’s a competitive advantage.
I’m seeing more and more Australian government tenders and large enterprise contracts that require a minimum of Essential Eight Maturity Level 2. If you can’t prove you are Restricting Administrative Privileges, you might find yourself locked out of lucrative deals.
The same goes for cyber insurance. The days of “tick-a-box” insurance are over. In 2026, insurers want to see logs. They want to see that you are using Entra ID PIM. They want to see that you are following the Principle of Least Privilege (PoLP). Those who do generally see lower premiums and much smoother claim processes if something does go wrong.
A Phased Roadmap for Success
You do not want to break your business on day one. A successful transition away from local admin rights usually follows a logical path-
- The Discovery Phase: You would be amazed at how many “ghost” admin accounts are lurking in the average Australian AD. Find them and kill them.
- The “Standard” Shift: Move your non-technical teams (Marketing, Sales, Admin) to standard accounts first. Their software needs are usually predictable and easy to manage via a self-service portal.
- The Technical Solution: For your IT and Dev teams, implement a PAM solution. Give them the ability to elevate when they need to, but make it a conscious, logged action.
- Continuous Review: Access control is not a set and forget project. People change roles, people leave, and requirements shift. Regular revalidation of who has what access is key to staying compliant.
The Cultural Shift – It’s About Safety, Not Control
At the end of the day, we need to change the narrative. Restricting Administrative Privileges is not about taking power away from employees. It’s about protecting them.
When an employee knows they are operating in a safe environment where a single mistake won’t bring down the whole company, they can actually work with more confidence. We’re building digital guardrails, not digital cages.
For Australian organizations, the goal is clear, we need to make it as hard as possible for an intruder to move through our systems. By tightening our grip on administrative access, we aren’t just checking a box for the ACSC; we are building a genuinely more stable and secure business.
Stay Tuned for Tech Updates
The landscape of Australian cybersecurity law and the Essential Eight is evolving faster than ever. From new ransomware reporting obligations to the shift toward phishing-resistant MFA, staying informed is your best defense. I’ll be continuing to break down these updates right here to help you navigate the 2026 threat environment with confidence.
Let’s Sort Out Your Access Strategy
I get it. The idea of stripping admin rights away from your team can feel like a headache waiting to happen. But it does not have to be a productivity killer. Whether you are trying to hit ACSC Maturity Level 2 for a government contract or you are just sick of the local admin security holes, I can help you build a roadmap that works for your specific culture.
Where do we start?
- Privilege Audit: Let’s find out exactly who has the keys in your environment right now.
- PAM Implementation: We can talk about setting up Entra ID PIM or LAPS to give you that Just-in-Time security without the friction.
- Compliance Strategy: I can help your leadership team understand why this shift is necessary so you do not have to fight the cultural battle alone.
DM me or get in touch for a confidential chat. No jargon, just straight-talking strategy on how to get your access controls where they need to be. Let’s make sure your “always-on” admin accounts do not become your biggest regret.