Strengthen Your Cybersecurity with Practical, Real‑World Guidance
Essential8Guy helps Australian organisations understand and implement the ACSC Essential Eight with clarity and confidence.
What We Do
Essential Eight education and guidance
Cybersecurity uplift and advisory
Practical implementation insights
Governance, risk, and compliance support

Internal vs External Essential Eight Uplift | An In
For most Australian organisations, the conversation around cybersecurity has matured. The focus is no longer on whether to adopt theWhy Microsoft Office Macro Settings are the Key to
Executive Summary: In the complex panorama of 2026 Australian business, we often obsess over high-tech AI breaches and shadowy foreignWhy 2026 is the Year Your Identity Becomes Your
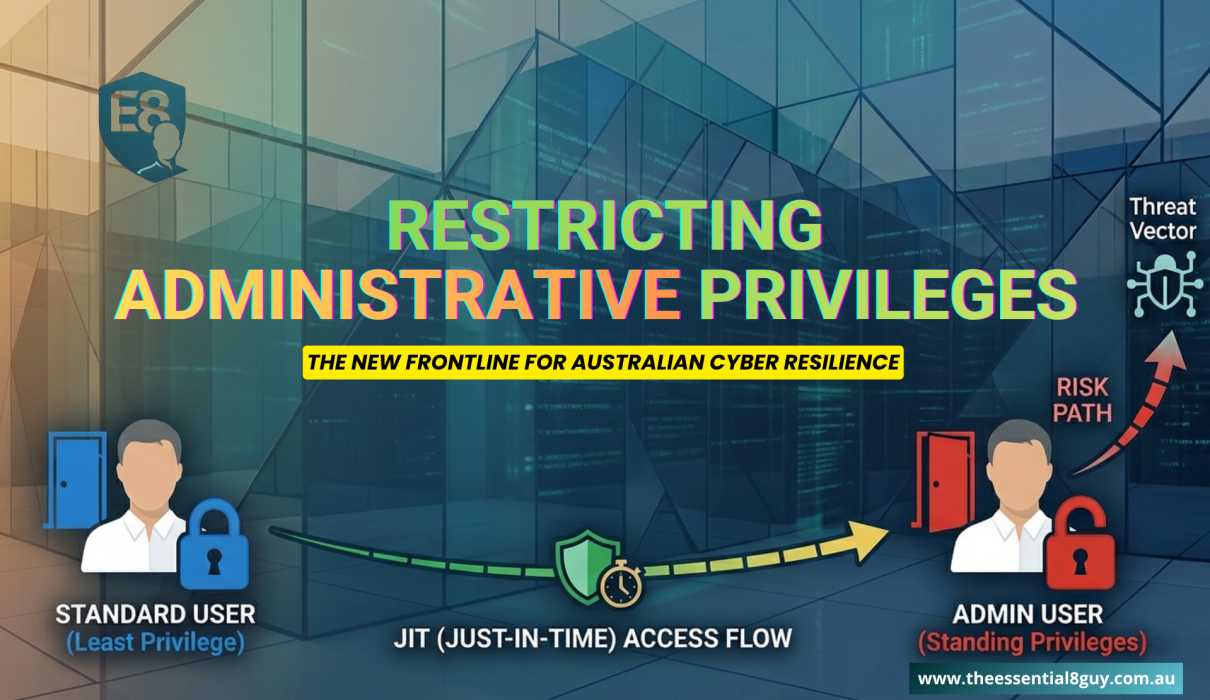
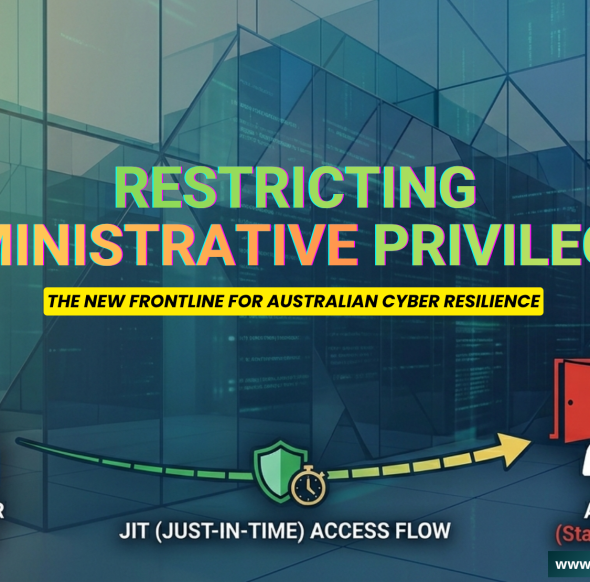
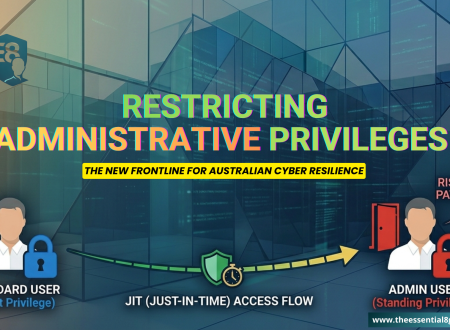
In March 2026, the Australian Signals Directorate (ASD) confirmed a significant shift in the threat landscape. For years, we focusedThe Privilege Paradox – Why Restricting Admin Rights is
In the world of Australian IT, Local Admin has historically been treated like a corporate birthright. For years, many organizationsEssential 8 Maturity Level 2 The New Resilience Standard
For the modern Australian decision-maker, CEOs, CISOs, and Business Owners alike, the conversation around cyber security has shifted. It isCybersecurity Advisory – Strategic Guidance for CIOs and CISOs
2026 brings an increasingly complex cybersecurity landscape. Organisations are navigating rapid digital transformation, hybrid cloud adoption, remote work expansion, andInternal vs External Essential Eight Uplift | An
- 4 Mins Read
For most Australian organisations, the conversation around cybersecurity has matured. The focus is no longer on whether to adopt the
Why Microsoft Office Macro Settings are the Key
- 5 Mins Read
Executive Summary: In the complex panorama of 2026 Australian business, we often obsess over high-tech AI breaches and shadowy foreign
Why 2026 is the Year Your Identity Becomes
- 6 Mins Read
In March 2026, the Australian Signals Directorate (ASD) confirmed a significant shift in the threat landscape. For years, we focused
The Privilege Paradox – Why Restricting Admin Rights
- 7 Mins Read
In the world of Australian IT, Local Admin has historically been treated like a corporate birthright. For years, many organizations
Essential 8 Maturity Level 2 The New Resilience
- 7 Mins Read
For the modern Australian decision-maker, CEOs, CISOs, and Business Owners alike, the conversation around cyber security has shifted. It is
Cybersecurity Advisory – Strategic Guidance for CIOs and
- 5 Mins Read
2026 brings an increasingly complex cybersecurity landscape. Organisations are navigating rapid digital transformation, hybrid cloud adoption, remote work expansion, and
The Macro Paradox – Closing the Office Backdoor
- 7 Mins Read
For many IT leaders, Essential Eight Microsoft Office Macro Settings are viewed as a relic of the early 2000s. A
ABOUT ME

Hariom Jindal
Hariom “Harry” Jindal is a Melbourne‑based cybersecurity specialist with more than 25 years of industry experience. He is Essential Eight Certified (CIT Canberra), ISACA CISM Certified, an ISO 27001 Lead Auditor, and a Certified Ethical Hacker. Harry also holds advanced certifications across Microsoft, Cisco, AWS, Google Cloud, and Red Hat.
POPULAR POSTS
Ask a Cybersecurity Expert
Not sure where to start or how to progress? Submit your query and receive clear, practical guidance from an experienced cybersecurity professional.