For most Australian organisations, the conversation around cybersecurity has matured. The focus is no longer on whether to adopt the framework, but on how far to take it and who should be responsible for driving that progress.
At this stage, the decision is rarely technical. It’s strategic. Should your Essential Eight uplift remain fully internal, or is external Essential Eight advisory required to reduce risk, validate maturity, and provide assurance to leadership? This is a common inflection point for organisations that are serious about cyber resilience and are no longer satisfied with “checkbox” compliance.
The Early Success Pattern in Essential Eight Implementation
Most organisations experience strong momentum during the early phase of their Australian cybersecurity journey.
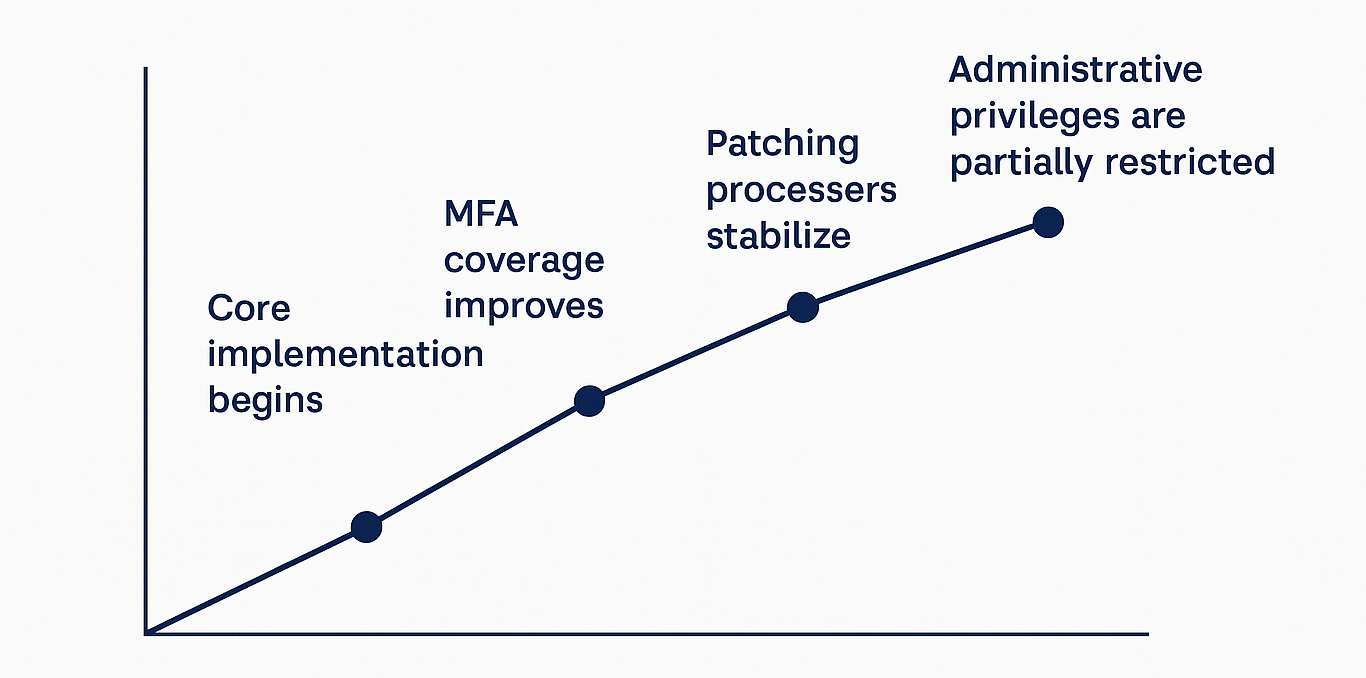
Internal teams, who have the most intimate knowledge of the network, successfully manage the initial Essential Eight implementation by-
- Rolling out MFA across core systems and email.
- Improving patching cycles for applications and operating systems.
- Restricting administrative privileges on standard workstations.
- Establishing and testing backup procedures for critical data.
At this stage, internal ownership works well. Early progress toward a baseline cybersecurity uplift is visible and measurable. For organisations targeting Essential Eight maturity Level 1, internal teams are often more than capable.
Related Insights
Before diving into the complex shift toward higher maturity levels, it is helpful to review the core technical pillars that often define the early stages of an uplift project-
- Essential 8 Maturity Level 2: The New Resilience Standard
- The Privilege Paradox: Why Restricting Admin Rights is the New Frontline
- Essential Eight Implementation: Turning Controls into Day-to-Day Practice
Where Internal Essential Eight Uplift Starts to Stall
As organisations deepen their maturity, expectations increase. Moving beyond baseline security requires a level of Essential Eight assessment rigor that internal teams often struggle to maintain alongside daily operations.
This is where many internal Essential Eight uplift efforts slow down or plateau. It’s rarely a skill gap; it’s an operational reality.
Teams often face:
- Legacy resistance: Systems that cannot be hardened without breaking functionality.
- Stakeholder friction: Internal users pushing back on new restrictions.
- The “Exception” Trap: Temporary security bypasses that quietly become permanent vulnerabilities.
The Conflict Built into Internal Maturity Assessment
A recurring issue in Australian cybersecurity discussions is role conflict. Internal teams are often expected to design, implement, validate, and report on the same controls.
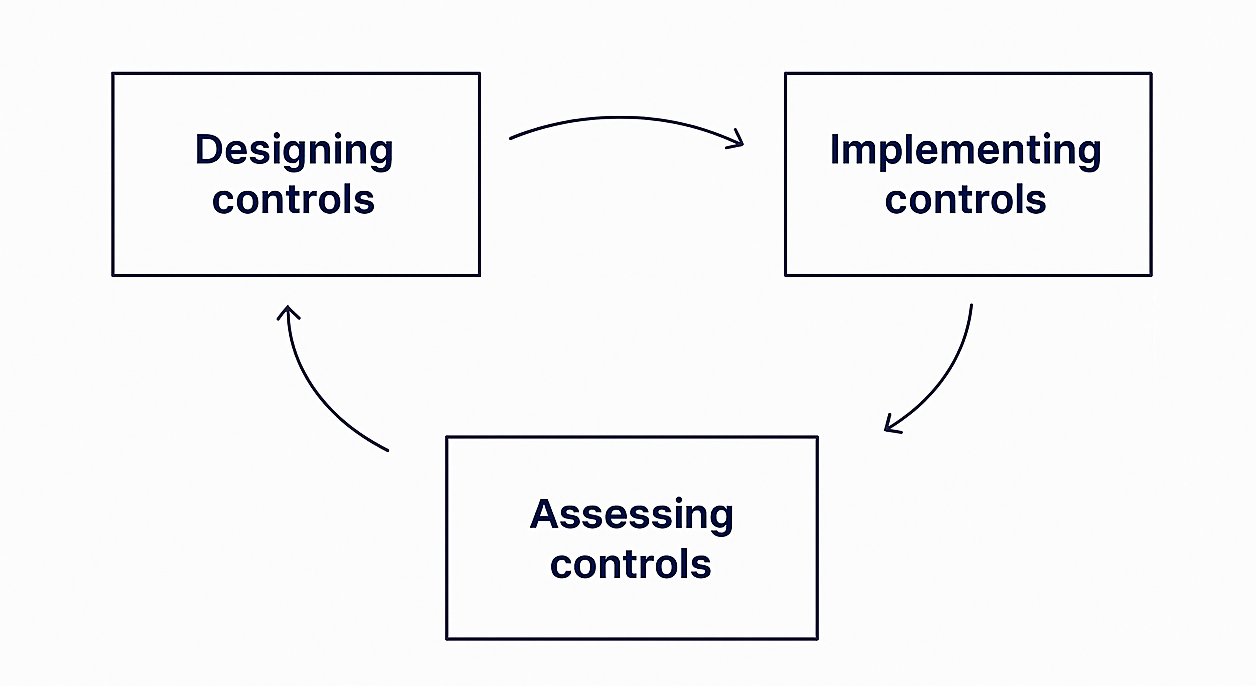
This is an inherently biased structure. Even the most well-intentioned teams can drift toward optimistic Essential Eight maturity scoring. Over time, reported maturity can diverge significantly from operational reality. This is precisely why many organisations seek external Essential Eight advisory support to provide an objective lens and ensure the ACSC Essential Eight standards are actually met, not just documented.
What External Essential Eight Uplift Actually Changes
External support is often misunderstood as simply “hiring consultants to do the work.” In reality, effective external support is about independent verification and clarity.
High‑value Essential Eight implementation support typically:
- Challenges assumptions that internal teams may no longer question.
- Validates control effectiveness beyond just checking the documentation.
- Aligns maturity claims with current ACSC Essential Eight expectations.
- Reframes technical posture into the business-risk language boards understand.
When External Support Makes the Most Sense
Across the Australian landscape, external expert involvement becomes a necessity when an organisation is:
- Targeting Maturity Level 2 or higher, where technical evidence is strictly audited.
- Preparing for regulatory scrutiny or upcoming government tender requirements.
- Engaging with high-value supply chains that require third-party assurance.
- Experiencing “plateaued” progress where internal projects have stalled.
Cost vs. Risk – Reframing the Decision
The decision is rarely about the invoice alone. The real comparison for a CEO or Board is…
Short‑term savings through internal delivery
Versus
Long‑term exposure from unvalidated assumptions.
Organisations that invest in external validation often avoid costly rework, reduce the impact of potential incidents, and crucially accelerate their cybersecurity uplift, reaching higher maturity levels far faster than those struggling internally.
Final Perspective
An Essential Eight uplift is not a binary choice. It is a decision about when independence and validation become a mechanical necessity for your business. Internal teams remain the backbone of your security, but external support becomes valuable when you are ready to defend, not just describe, your maturity.
Making that decision deliberately is a true sign of cyber leadership in the modern Australian market.
Take the Next Step
If you are currently evaluating your Essential Eight uplift strategy and want to pressure-test whether your current approach would hold up under independent scrutiny, I regularly share practical insights drawn from real Australian environments.
DM me or stay connected for future updates—no hard sell, just informed perspective on achieving true cyber resilience.


